Our Research Areas
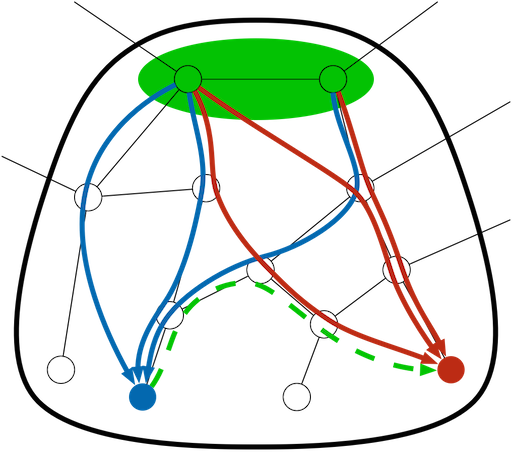
SCION
SCION is the first clean-slate Internet architecture designed to provide route control, failure isolation, and explicit trust information for end-to-end communications. SCION separates ASes into groups of independent routing sub-planes, called isolation domains, which then interconnect to form complete routes. Isolation domains provide natural isolation of routing failures and human misconfiguration, give endpoints strong control for both inbound and outbound traffic, provide meaningful and enforceable trust, and enable scalable routing updates with high path freshness. As a result, our architecture provides strong resilience and security properties as an intrinsic consequence of good design principles, avoiding piecemeal add-on protocols as security patches. Meanwhile, SCION only assumes that a few top-tier ISPs in the isolation domain are trusted for providing reliable end-to-end communications, thus achieving a small Trusted Computing Base. Both our security analysis and evaluation results show that SCION naturally prevents numerous attacks and provides a high level of resilience, scalability, control, and isolation.

Public Key Infrastructures
Today's PKIs suffer from many severe problems - CA compromises can affect any site in the Internet due to their almost unrestricted global authority, most users cannot competently assess the trustworthiness of CAs without restricting access to many HTTPS sites, and revocation of certificates and misbehaving CAs is difficult and ineffective. Our research focuses on addressing these problems through a variety of approaches. We build on log-based PKI proposals such as Sovereign Keys and Certificate Transparency, using public, append-only logs to monitor CA behavior and ensure that certificates are issued according to domain-specified policies. We also leverage public logs to handle revocations and key updates in response to events such as key loss or compromise. On a larger scale, we are redesigning the global PKI infrastructure for routing, naming, and end-entity certification (such as TLS) to further restrict global CA authority without hindering access to HTTPS sites worldwide.
Distributed Denial of Service Defenses
Distributed Denial of Service (DDoS) attacks are increasingly becoming commonplace in today's Internet. Attackers, commandeering thousands of compromised systems distributed across the globe, possess large amounts of resources to deny service to even large service providers. We aim to propose lightweight, deployable defenses that can assist in preventing or mitigating the impact of DDoS attacks.
High-speed Anonymous Communication
This project considers the scalability issues of current-generation anonymous networks such as Tor. By requiring relays to keep state for each anonymous connection, Tor suffers from scalability limitations. We are designing next-generation anonymous networks that provide anonymity features as part of their default routing architecture. By leveraging source-selected routing architectures such as SCION, we can offer highly scalable and highly efficient end-to-end anonymous routing that does not need to keep per-flow state on routers. Our initial experiments show that this design scales to millions of nodes and can forward traffic at speeds upwards of 93 Gbits/s.